Authenticating with OpenID Connect
Published 28 March 2024
Redgate Monitor supports authentication via OpenID Connect (OIDC), allowing you to integrate with identity providers such as Microsoft Entra ID or Okta. You can choose between three authentication modes:
- Authorization code flow (PKCE) with client secret
- Authorization code flow (PKCE) with private key JWT (using a certificate from a file path or from Windows Certificate Store)
- Implicit flow (no client authentication)
After OIDC authentication is enabled, all users must authenticate via your identity provider.
An Administrator user can restrict which servers users can access, in the same way as when Active Directory authentication is used.
If you plan to use Microsoft Entra ID or Okta as your OIDC identity provider, please follow our detailed guide:
Configuring Identity Provider
First, register Redgate Monitor as an application (client) in your OIDC identity provider.
Here's a checklist for configuring your OIDC identity provider:
- Specify the redirect URL for Redgate Monitor as
https://yourRedgateMonitorHost.com/openidconnectaccount. This is the URL that the Identity Provider will use after a user is authenticated - Specify the sign-out URL for Redgate Monitor as
https://yourRedgateMonitorHost.com/signout-callback-oidc. This is the URL that the Identity Provider will use when a user attempts to sign-out - Enable either implicit flow or authorization code flow, depending on which authentication method you intend to use
- If using Private Key JWT, ensure the identity provider holds the public key
Redgate Monitor will make the OIDC authorization request using the "openid profile" scopes, and the token grant-type should be implicit with only an ID token enabled.
When configuring your identity provider, take note of information like the ClientID (sometimes referred to as ApplicationId) and the metadata endpoint that you will need to finish the setup in Redgate Monitor itself.
Group Claim Limitations
It is common that OIDC providers will limit the number of groups that are included in an OIDC token for performance reasons. If your organization's identity provider contains a large number of groups, then you may need to do some additional configuration inside your identity provider before it can be used with Redgate Monitor.
When using Microsoft Entra ID as your provider, the limit is 200. It is recommended to set the returned group types in the token to Groups assigned to the application so that only the groups relevant to Redgate Monitor are included. See here for information on how to do this.
When using Okta as your provider, the limit is 100. You must use the Groups claim filter field when setting up your OIDC token for integration with Redgate Monitor to ensure it does not exceed this limit. See the documentation for more information.
Other providers may have similar limits on the number of groups. We recommend you consult the official documentation of your provider regarding group claims if you think this may be an issue for your organization.
Switching to OIDC authentication
OIDC is only supported with HTTPS enabled. See here for more information on how to set up Redgate Monitor in IIS and here on how to set up in the default web server (Kestrel). When using IIS, application initialization should also be configured as described here.
Only users with the Administrator role can switch Redgate Monitor to OIDC authentication.
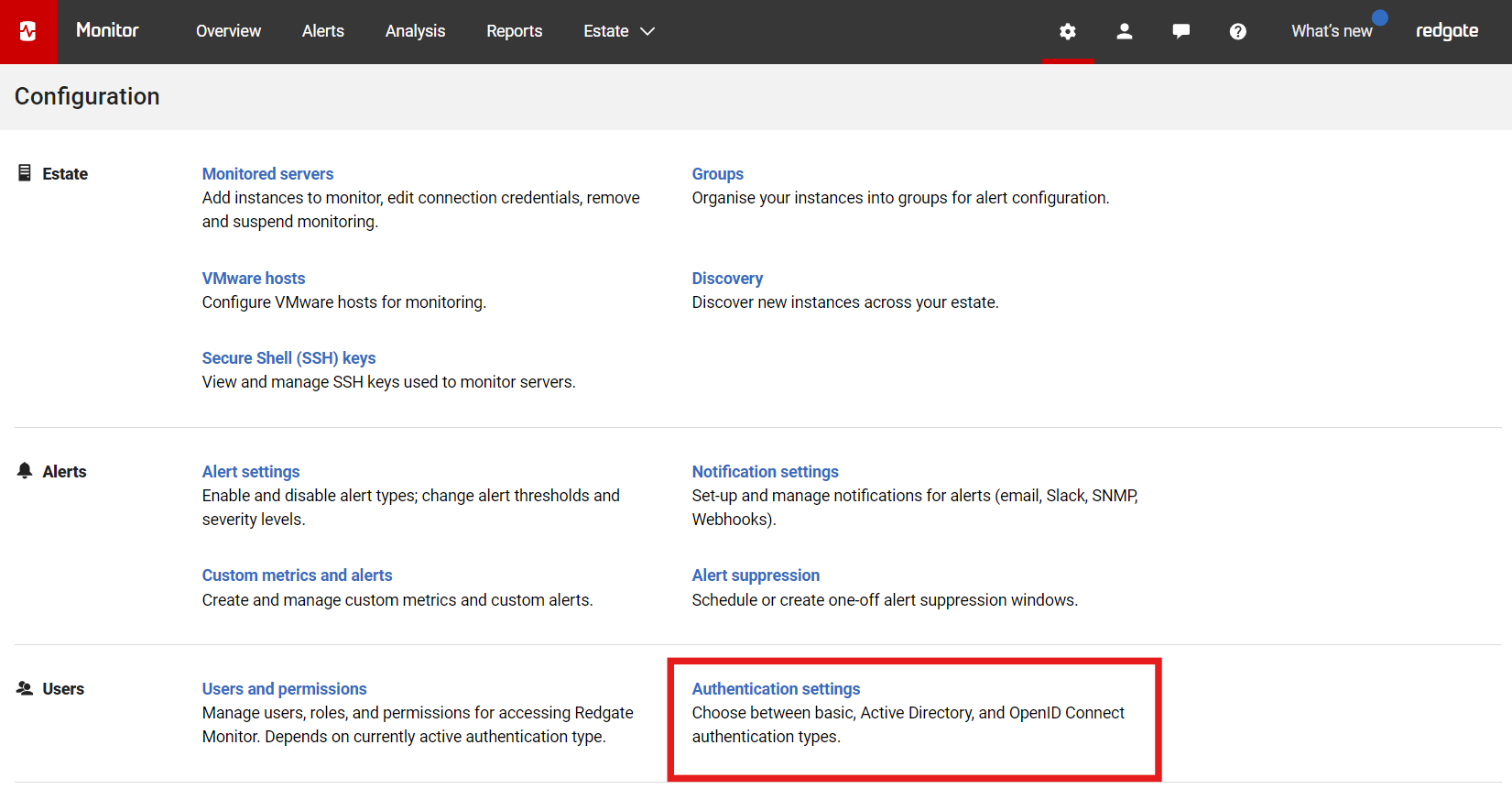
In the Configuration page, under Users, click Authentication settings:
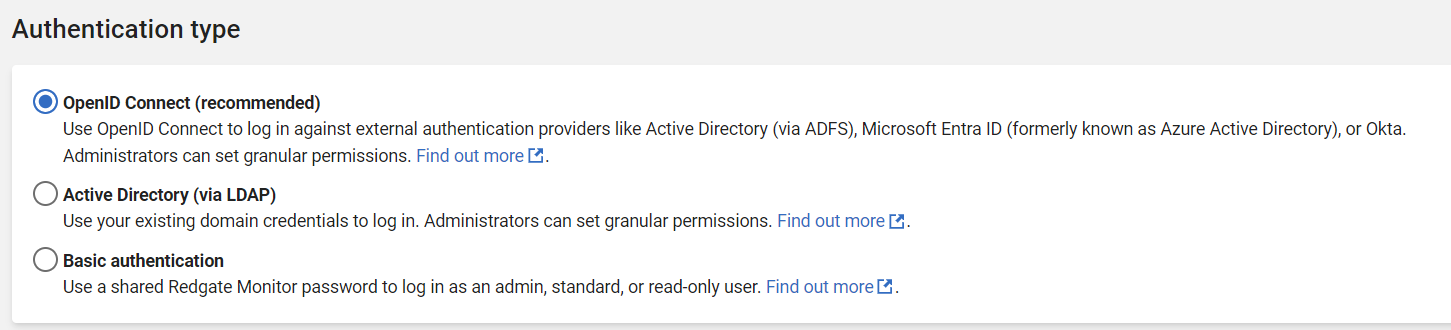
Select Use OpenID Connect:
Provide the details requested in the dialog:
Authority URL
Enter the URL to reach your authentication provider. E.g. https://login.microsoftonline.com/[tenant-id]/v2.0. This value will also be used to verify the issue of your ID token through an exact match (including any trailing slashes). If you have a metadata endpoint (e.g. ending in .well-known/openid-configuration) it should be the URI before that ending).
Client ID
Enter the Client ID as returned by your Identity Provider when you registered Redgate Monitor as an application (client) in your OIDC identity provider.
Flow type
Select either:
- Authorization code flow with PKCE (you will be prompted to specify a Client authentication method)
- Implicit flow (no client authentication - go to Claims)
Client authentication method
Select either:
- Client secret (you will be prompted to enter a 32-character alphanumeric OIDC key)
- Private key (you will be prompted to specify a Certificate source)
Certificate source
For authorization code flow with private key JWT, you will be prompted to specify either:
- a file path to a .pfx/.p12 certificate
- the Website OS certificate store details (thumbprint, store name and store location)
Note that the certificate store option is currently only supported on Windows. If you are using a non-Windows platform, you will be prompted to use the file path option.
Claims
Enter the Username claim name or Group claim name. This is the name of a claim that will be supplied by your identity provider after a user logs in and Redgate Monitor will use that information to identify which user logs on.
Common examples of claim names to be used for the Username claim name field value are email or preferred_username. For the Group claim name a common example is groups.
Toggle ID token on logout
Define whether Redgate Monitor should send ID token on logout. This will depend on which identity provider you will be using and is not required by default. However, some providers like Okta require the ID token to be sent back when a logout is requested.
Specify an administrator
Add an Administrator user or group. Normally, it is the username of the Administrator of Redgate Monitor or a name of a user group to which an Administrator belongs. It needs to map to the value returned in the field specified in Claim name before.
We recommend you create an administrator group and specify this as the administrator account. This means you can add more users to the administrator group in your identity provider instead of configuring new users in Redgate Monitor.
In case of any problems or misconfiguration, switch back to basic authentication in Redgate Monitor's Configuration > Authentication settings page.
Configuring OIDC scopes
By default, Redgate Monitor will use openid and profile as the scopes for the authentication request. Some authentication providers may require additional scopes to return specific data like groups or an email field. You'll be able to configure these scopes by running the following these steps:
- Connect to your Redgate Monitor data repository.
Run the following script. This will add additional scopes on to the default
openidandprofilescopes that Redgate Monitor uses.Edit OpenID scopes used by Redgate Monitor
--For repository on SQL Server INSERT INTO [settings].[KeyValuePairs] VALUES ('OIDC-Scope', '<AdditionalScope> <OtherAdditionalScope>', 'STRING') --For repository on PostgreSQL with TimescaleDB INSERT INTO settings.key_value_pairs (key_name, key_value, key_value_type) VALUES ('OIDC-Scope', '<AdditionalScope> <OtherAdditionalScope>', 'STRING')- Restart Redgate Monitor’s website.