SQL Audit
Published 02 October 2025
This tab displays actions related to permission changes using SQL Audit. Since we are using SQL Audit to detect these events, it does not guarantee that the operation completed successfully or that a change was made. It indicates that this action was executed in SQL Server.
This feature is in preview, so its behavior will evolve. Please note that any data collected during this phase might not be retained.
By default, the maximum number of audit files retained is 5, and each audit file is set to 100 MB. Redgate Monitor cannot ensure the security of the Audit files or tampering with the Monitor data repository.
Action being Audited:
Redgate Monitor audits the following actions:
- Creating, modifying and deleting a security principal (CREATE, ALTER, DROP).
- Creating, modifying and deleting a database principal (CREATE, ALTER, DROP).
- Adding and removing server principals from a server role.
- Adding and removing database principals from a database role.
- Changing a database user's login (
EXEC sp_change_users_login 'Update_One'...). - Auto-changing a database user's login (
EXEC sp_change_users_login 'Auto_Fix'...). - Adding and removing permissions from a server principal (GRANT, DENY, REVOKE).
- Adding and removing permissions from a database principal (GRANT, DENY, REVOKE).
- Changes to ownership of a server principal (ALTER AUTHORIZATION ON).
- Changes to ownership of a database principal (ALTER AUTHORIZATION ON).
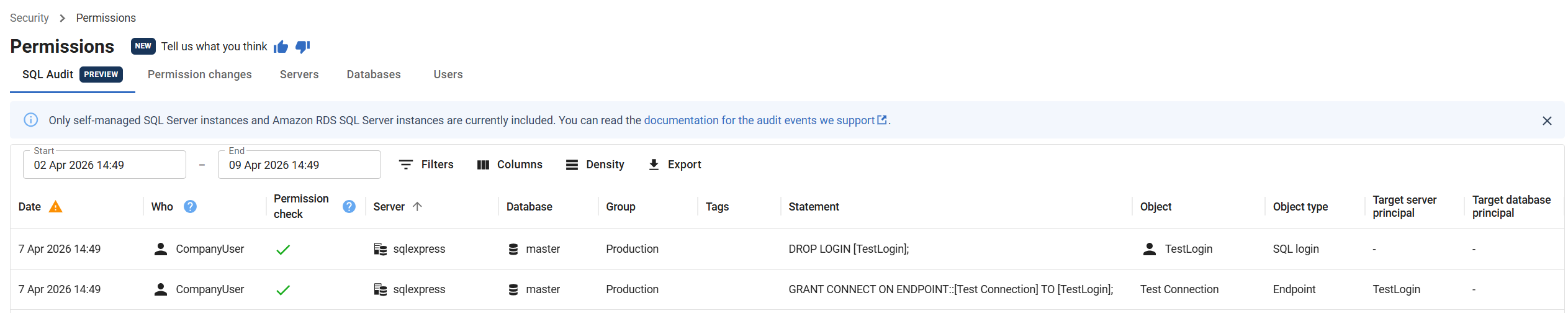
Below is a definition for each column on the SQL Audit grid.
- Date: The date and time that the audited event was executed.
- Who: The server principal that executed the action. Impersonated login will appear within brackets if impersonation was used when executing the action. Maps to the session server principal in SQL Audit.
- Permission check: Determine if the session server principal had appropriate permissions to run the action. Maps to the "succeeded" column in SQL Audit.
- Server: The server name.
- Database: The database name.
- Group: The name of the group that the server is associated with.
- Tags: A list of current tags for the server.
- Statement: The SQL script that was run when executing the audit event.
- Object: The server or database security principal affected by the audit event.
- Object type: The type of the security principal.
- Target server principal: The target server level principal of the action.
- Target database principal: The target database level principal of the action.
SQL Audit on Amazon RDS
For information on setting up SQL Audit on Amazon RDS, visit our Setup Amazon RDS SQL Audit page.
Permissions required for enabling SQL audit
For SQL Server 2022 or later, the minimum permissions required are ALTER ANY SERVER AUDIT and VIEW SERVER SECURITY AUDIT. These permissions can be granted using the SQL statements below.
GRANT ALTER ANY SERVER AUDIT TO [sql_monitor_account]; GRANT VIEW SERVER SECURITY STATE TO [sql_monitor_account];
For SQL Server 2019 or earlier, the CONTROL SERVER permission is the minimum required permission.
GRANT CONTROL SERVER TO [sql_monitor_account];
If the user has the sysadmin role then no additional permissions need to be granted.
The minimum required permissions are ALTER ANY SERVER AUDIT and SELECT on msdb.dbo.rds_fn_get_audit_file. These permissions can be granted using the SQL statements below.
GRANT ALTER ANY SERVER AUDIT TO [sql_monitor_account];
USE msdb; GRANT SELECT ON OBJECT::msdb.dbo.rds_fn_get_audit_file TO [sql_monitor_account];
If the user has the sysadmin role then no additional permissions need to be granted.
Known issues
SERVER_OBJECT_PERMISSION_CHANGE_GROUP are not captured. This means that permission grants/revokes/denies on server objects will not show up in the SQL Audit tab. To ensure complete audit coverage, make sure you have installed CU19 or later.