Configuration
Published 07 December 2022
To view configuration settings, use the Config tab of the Admin Console.
Changing Settings
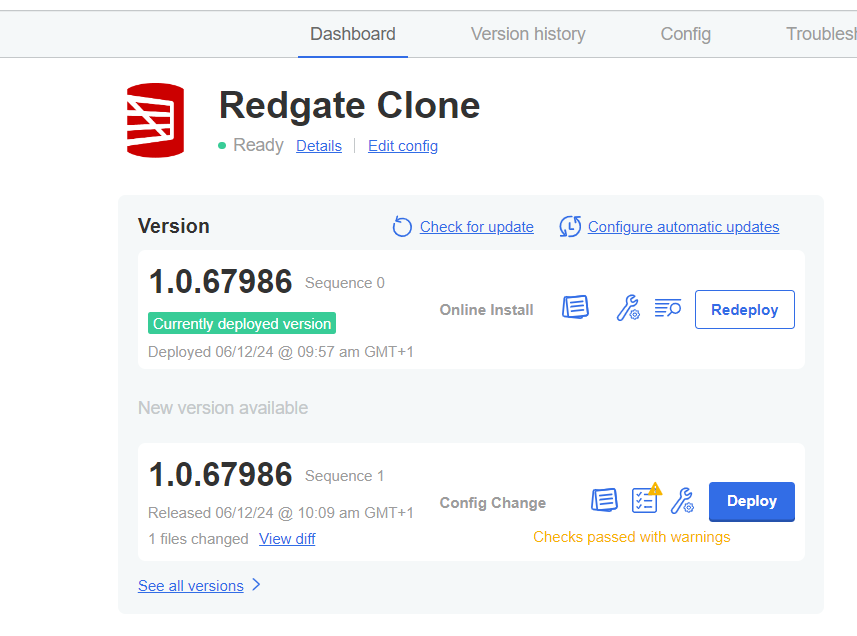
Once you have finished editing your settings, click Save config. This will create a new version of the application that you can deploy to your cluster when you are ready.
You can deploy your new version in the same way that you deploy application updates. See Update Redgate Clone for more information.
Your changes will not take effect until the new version is deployed.
Available Settings
| Section | What |
|---|---|
Authentication: Token-based | Configure authentication parameters for the various components of Redgate Clone when used in a token-based fashion. This is intended for CI/CD pipeline usage. |
Authentication: OpenID Connect (OIDC) | Settings that enable our authentication mechanisms to talk to an existing identity provider using OIDC (e.g. Azure Active Directory). |
Data Image and Data Container Storage Settings (Embedded, Managed Kubernetes) | Specify the path to the attached storage disks, where data images and data containers are going to be stored. |
Communications Security | Settings that control how the host should be accessed from outside the cluster in a secure way (TLS). |
Backup Storage Settings | Specify where the database backups are located so they can be accessed during data image creation. |
Default Clone Lifetimes | Settings that control how long data images and data containers will persist for by default. |
Data Container Port Range | Settings that control the port range that will be used to expose data containers. |
Advanced Settings: Resource Limit & Request Configuration | Settings that enable fine-grained control over memory and CPU usage of data containers for each database engine. |
Advanced Settings: Monitoring | Settings that control access to the monitoring dashboards that ship with Redgate Clone by default. |
Advanced Settings: Backup Size Allocation | Settings that control allocation of additional persistent volume capacity for data images on top of existing backup size. |